What is Yokogawa’s lifecycle approach for Cybersecurity Management?
We are in a new age of controlling cybersecurity risks. The way we work is changing. The connectivity is increasing, and the cybersecurity threat landscape is changing with it. To help our customers continue their industrial operations safely and securely, Yokogawa provides comprehensive cybersecurity solutions and services based on defense in depth strategy. We focus on delivering long-term lifecycle services while understanding customers' challenges and working continuously for improvements in a close partnership. Yokogawa follows one overall objective: to minimize risk and maximize corporate values according to our self-commitment as a lifecycle value partner. Yokogawa aims to become your #1 trusted partner and achieve long-term, stable, and secure operations.
Yokogawa is seeing customer's plants as important as a human body.
-
Security Program
Yokogawa’s cybersecurity services take a lifecycle approach to help customers control the security risks and manage them to achieve the highest business continuity plan throughout the plant’s entire lifecycle.
-
Cybersecurity Consulting Services
Yokogawa’s comprehensive Cybersecurity Consulting Services help customers deploy proper security solutions for their plants to ensure safe operation while adapting to new technology for achieving higher efficiency and productivity.
-
Product Security
Yokogawa has established the basic policy and measures criteria for the security control of products.
-
OpreX IT/OT Security Operations Center (SOC)
Managed IT/OT cybersecurity services for threat detection and remediation
Zasoby
Rousselot Ghent won Belgium Factory of the Future Award. Yokogawa has supported Rousselot with automation systems since 1993.
Data of 20,000 tags gathered by Exaquantum helped to find the ideal production parameters.
A virtual network system that securely connects OT-IT built on existing network resources.
Yokogawa experts monitor the network remotely like customer's information system department.
At the 2015 ARC Industry Forum in Orlando, Florida in February, Yokogawa announced a collaboration with Cisco to deliver Shell’s SecurePlant initiative, a comprehensive security management solution for plant control systems jointly developed by Cisco, Yokogawa, and Shell. This report explains how Cisco Systems and Yokogawa worked with Shell to co-develop the company’s “SecurePlant” cybersecurity solution for its control systems.
Network and system security is now a necessity in process automation industry. YOKOGAWA provides a service lifecycle solution for cyber security to ensure that the security measures and deployments are continuously enhanced, monitored and inspected.
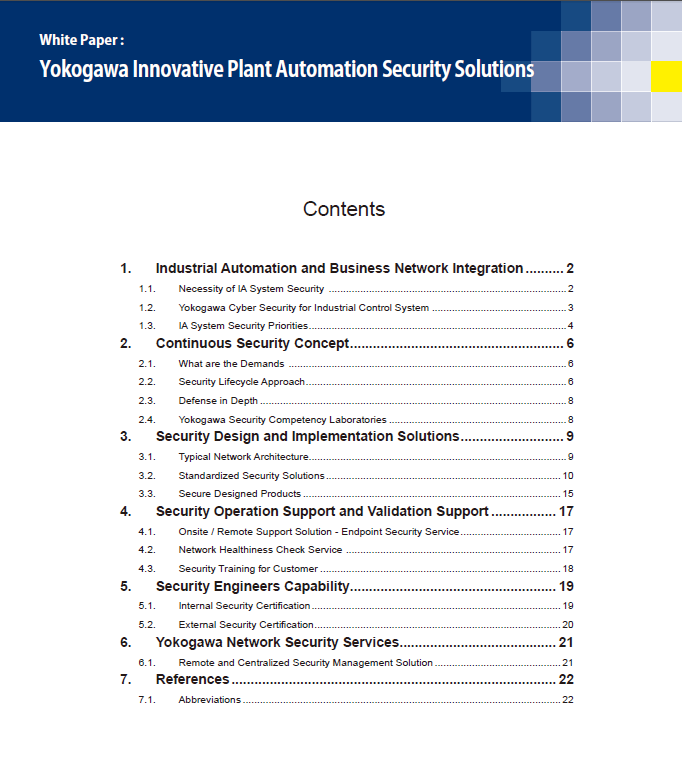
This white paper explains the details of the security design, implementation, operation and validation solutions from the technical perspective.
Watch for a backdoor cyber security assualt. The Juniper Networks incident in December 2015 changed how industry looks at device security as hackers exploit deliberate weaknesses being installed into software. End users, integrators, and device manufacturers need to adapt and prepare for this new reality. Follow these cyber security steps.
Process automation systems are increasingly connected to IT systems and the outside world, introducing cybersecurity concerns, which can be addressed using techniques such as software-defined networking and monitoring services.
Supervisory control and data acquisition (SCADA) systems have been part of the process industries for many decades and cyber security measures need to grow as technology advances. SCADA systems are used in oil and gas pipeline and other remote control and monitoring applications, such as electrical transmission and distribution, and water/wastewater.
Downloads
Broszury
Wideo
How vulnerable is your plant to cyber attack? As industrial cyber attacks evolve, plant security has become a pressing challenge.
Wiadomość
-
Informacja prasowa maj 8, 2015 Yokogawa Promotes GICSP Training to Enhance Plant Safety
-
Informacja prasowa sty 29, 2020 Yokogawa Obtains ISASecure SDLA Certification for Control System Development Process
Plant cyber security support throughout the product development lifecycle
Szukasz dodatkowych informacji na temat naszych pracowników, technologii i rozwiązań?
Kontakt